Multi-layered Internal Network Security Securify Engine
Intelligent and Continuous
Internal Threat Prevention
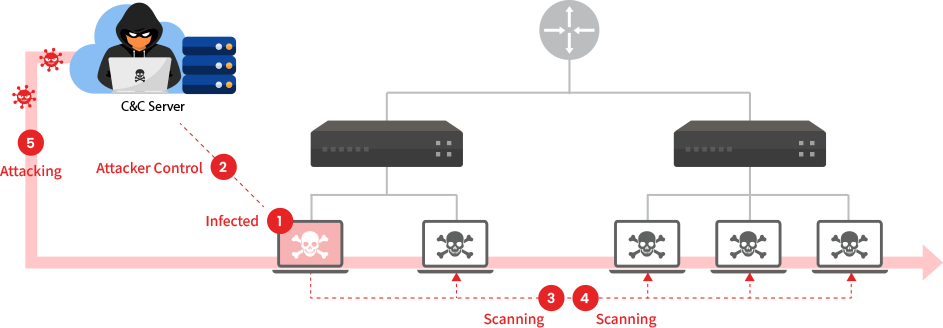
Attackers infiltrate internal networks through multiple entry points and increasingly
sophisticated techniques. Once inside, they infect systems with malware, explore to identify
targets, and spread laterally across the network to achieve their ultimate objectives.
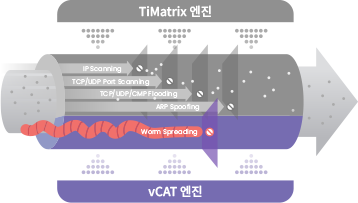
PIOLINK TiFRONT Security Switch leverages multiple security engines to build a multi-layered
defense architecture within internal networks. This enables proactive and preemptive
responses to threat propagation, effectively containing and mitigating security incidents before they escalate.
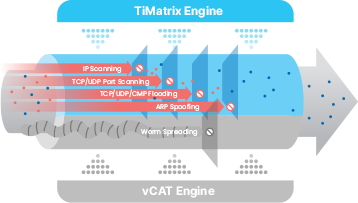
- TiMatrix
Malicious Traffic Blocking Engine
-
Proprietary security algorithm based on Frequency Matrix
Automatically identifies and blocks only malicious traffic without administrator intervention
Responds to zero-day threats without relying on signatures
Maintains full line-rate performance even while security functions are active
- vCAT
Worm Propagation Prevention Engine
-
Detects and blocks new attacks through continuous profile updates
Automatically blocks and reports lateral movement attempts from infected internal devices
Provides forensic-ready data for incident analysis
Detects and blocks worm propagation attacks
- CTI
Malicious Website Blocking Engine -
Utilizes data collected by the PIOLINK Cyber Threat Intelligence (CTI) team and multiple threat detection channels
Provides in-depth analysis to support threat prevention and rapid policy creation
Identifies and blocks IPs communicating with attackers’ C2 servers
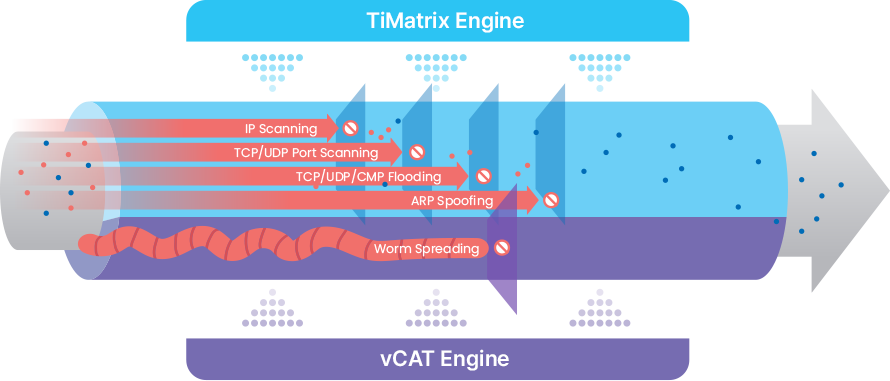
Malicious Traffic Blocking Engine

As network traffic volumes continue to grow, switches must process increasingly complex traffic with speed and stability. TiMatrix, the core security service of TiFRONT, selectively detects and blocks malicious traffic generated by user endpoints. With a hardware and logical separation between switching and security engines, TiMatrix delivers robust security services without traffic latency. By detecting and controlling malicious traffic within the internal network, TiMatrix prevents secondary damage caused by outbound malicious traffic and ensures overall network stability.
- Selective Blocking of Malicious Traffic
-
Only malicious traffic is blocked, while legitimate traffic remains unaffected, ensuring business continuity.
(Protocol Anomaly, Flooding, Scanning, Spoofing, SMB, etc.)
- Protection Against Major Attack Types
- Blocks internal ransomware and malware propagation, and controls DoS/DDoS traffic generated by infected internal hosts to protect the network.
- Comprehensive L2–L4 Packet Analysis
- Analyzes MAC addresses, IP addresses, protocols, service ports, intervals, counts, and packet metadata to deliver precise and fine-grained security.
- Zero-day Threat Response
- Detects and responds immediately to new threats by analyzing traffic and metadata using a Frequency Matrix–based model, without signatures.
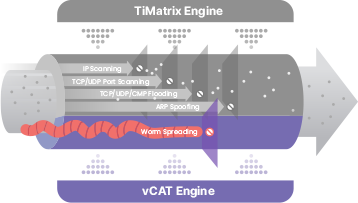
Worm Propagation Prevention Engine

vCAT is an active security engine designed to detect and block malware infections and internal lateral movement. It deploys vTraps, decoy systems disguised as real hosts on the security switch, and monitors scanning attempts or access to these traps to identify malicious activieies. Because attackers are unaware of the existence of vTraps, any attempt to access them is treated as anomalous behavior. This allows vCAT to analyze attacker intent and capture early-stage intrusion attempts.
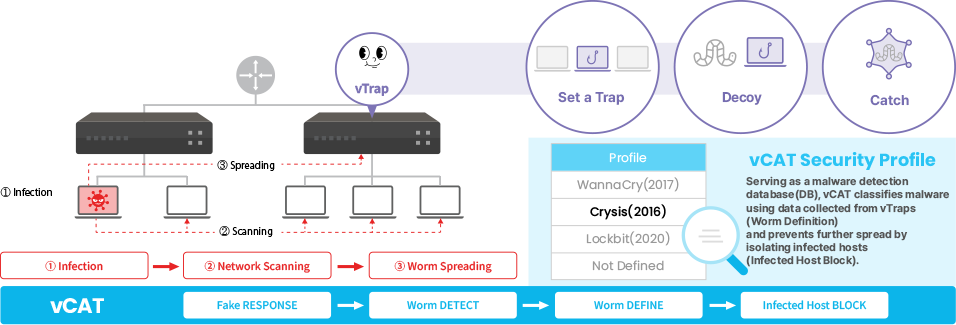
vCAT Security Engine Operation Process
vCAT lures malware into vTraps, analyzes its behavior, and immediately isolates the
accessing host. Through this process, vCAT proactively prevents internal malware
propagation, ensuring a secure and resilient network environment.
-

Fake Response
The security switch configures vTraps and responds when malware attempts to access them. Attackers perceive vTraps as real hosts and are unknowingly lured into interaction. #vTrap #Malware Luring
-

Worm Detection
Attack types lured to vTraps are identified and analyzed. Packets generated during malware access attempts are captured and analyzed to distinguish malware types and behavioral characteristics. #Malware Analysis #Packet Pattern Analysis
-
Worm Definition
Profiles are predefined sets of detection criteria that enable the switch to identify and analyze various threat types. Continuously updated malware databases play a critical role in detecting and analyzing new and variant malware threats. #Malware Database “Profiles” #Advanced & Unknown Threat Detection
-

Infected Host Block
TiFRONT Security Switch isolates anomalous IPs attempting to access vTraps, preventing further attack propagation. Internal users are also blocked if they access vTraps, in accordance with the Zero Trust security model that assumes no implicit trust within the network. #Real-time Detection & Blocking #Internal Spread Prevention #Zero Trust Implementation
Five Stages of Cyber Attacks
- 01Initial
Intrusion
Attempt - 02Successful
Infection - 03Internal
network
exploration - 04Lateral
Movement - 05Objective
Achievement
Five Stages of Cyber Attacks
Cyber attacks typically follow these five stages, progressing from initial intrusion to final objective completion.
Key Features of the vCAT Worm Propagation Prevention Engine
-

Overcoming Threshold-Based Limitations
Threshold-independent detection: vTrap is deployed as a decoy meticulously disguised to appear as a legitimate, existing system. Any access to this address is inherently considered abnormal and can be detected regardless of threshold settings.
Detection of low-and-slow attacks: Even slow, distributed scans below threshold levels are detected upon a single vTrap access.
Behavior-based analysis: Analyzes actual packet behavior and malware characteristics for accurate detection
-

Defense Against Advanced and Unknown Attacks
Detection and learning of unknown threats: New attack patterns are collected and analyzed through vTraps, automatically updating the threat database
Attacker behavior-based detection: Detects threats based on actual attacker actions such as scanning, intrusion, or malware delivery
Attacker profiling and preemptive defense: Identifies repeated access attempts and provides early warnings of insider threats or long-term infiltration attempts
-

Real-time and Adaptive Defense
Real-time Detection and Blocking: Immediately isolates the host from the network upon access to a vTrap, preventing further damage and lateral spread.
Attack Trend Analysis and Enhanced Response Strategies: Uses attack data collected from vTraps to refine security policies and adjust thresholds of the TiMatrix security engine.
-

Insider Threat Detection & Zero Trust Reinforcement
Internal Network Threat Detection: Immediately detects anomalous behavior from insider threats or infected PCs when internal users attempt to access a vTrap.
Zero Trust Environment Implementation: Enforces the Zero Trust security model by verifying and validating every access within the network.
Build a ‘Multi-layered Defense Architecture’ with TiMatrix + vCAT
By combining the mechanisms of TiMatrix and vCAT, TiFRONT delivers a comprehensive security
environment that continuously monitors real-time threats through behavior analysis, proactively defends
against targeted attacks, and supports post-incident analysis through intrusion data analytics.
| TiMatrix Security Engine (Malicious Traffic Blocking) |
vCAT Security Engine (Worm Spread Prevention) |
|
|---|---|---|
| Security Engine Mechanisms |
Detects and selectively blocks only malicious traffic through behavior analysis Detection and blocking of new threats Detects and blocks threats in real time without affecting switch performance, with automatic release when threats subside Allows security levels and thresholds to be tailored to the organization’s network environment, minimizing false positives |
By deploying vTrap, which is engineered to appear as a legitimate system, targeted attacks are deliberately lured Attacker intent analysis and early intrusion attempt detection Early detection of attacks leveraging unknown vulnerabilities Proactive defense against zero-day and targeted attacks |
| Attack Type Coverage |
Protection against Protocol Anomaly, Flood, Scanning, and Spoofing attacks |
Provides profiling of targeted attacks based on intrusion attempt data (e.g., WannaCry, LockBit, NotPetya) |
| TiMatrix 보안엔진 (유해 트래픽 차단) |
|---|
| 보안엔진 매커니즘 |
|
행위 분석 기반으로 유해트래픽만 선별적으로 탐지·차단 새로운 위협도 탐지·차단 가능 스위치 성능에 영향을 주지 않으면서도 실시간으로 위협을 탐지 및 차단하고 자동으로 해제 조직의 네트워크 환경에 맞도록 보안 등급과 임계치를 설정하여 오탐을 최소화 |
| 공격 유형 대응 |
Procotol Anomaly, Flood, Scanning, Spoofing 공격 대응 |
| vCAT 보안엔진 (웜 확산 차단) |
|---|
| 보안엔진 매커니즘 |
|
공격자가 실제 시스템으로 착각하도록 설계된 vTrap을 배치하여 타깃형 공격을 유도 공격자의 의도를 분석하거나 초기 침입 시도를 탐지 알려지지 않은 취약점을 악용한 공격에 대해서도 초기 징후 포착 가능 제로데이 및 타깃형 공격에 대한 선제적 방어 |
| 공격 유형 대응 |
침입 시도 데이터를 분석하여 타깃형 공격에 대한 프로파일링 제공 (WannaCry, Lockbit, NetPetya 등) |
 TiFRONT Security Switch
TiFRONT Security SwitchComprehensive Threat Detection and Response : Continuously monitors anomalous activities across the entire network in real time through behavior-based analysis and proactively defends against targeted attacks.
Proactive Prevention & Post-incident Analysis : Provides real-time attack defense based on thresholds and supports proactive prevention and post-incident analysis through intrusion attempt data analysis.
Efficiency : Delivers maximum security effectiveness at minimal cost through a network switch–based architecture.
